Wikipedia:WikiProject on open proxies
| WikiProject on open proxies |
|---|
|
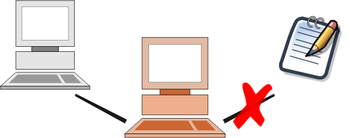
The WikiProject on open proxies seeks to identify, verify and block open proxies and anonymity network exit nodes. To prevent abuse or vandalism, only proxy checks by verified users will be accepted. All users are welcome to discuss on the talk page, report possible proxies, or request that a blocked IP be rechecked.
|
Reporting
[edit]Please report IP addresses you suspect are open proxies below. A project member will scan or attempt to connect to the proxy, and if confirmed will block the address.
| Before reporting any suspected open proxies here, please remember that not all vandals are open proxies and vandals should not get an automatic check here; remember that it takes the volunteers here about 5-10 minutes to give a request a thorough check. |
| File a new report here | ||
| I. | For block requests:
Verify that the following criterion has been met:
For unblock requests:
Verify that the following criteria has been met:
| |
| II. | For block requests
Replace "IP" below with the IP address you are reporting. For unblock requests
Replace "IP" below with the IP address you are reporting. | |
| III. | Fill out the resulting page and fill-in the requested information. | |
| IV. | Save the page. | |
Verified Users/Sysops Templates
|
|---|
|
Requests
[edit]| This page has an administrative backlog that requires the attention of willing administrators. Please replace this notice with {{no admin backlog}} when the backlog is cleared. |
| Index |
165.85.64.0/22
[edit]![]() – A proxy checker has requested a second opinion on this case.
– A proxy checker has requested a second opinion on this case.
Reason: Amazon AWB. 165.85.64.0 - 165.85.66.255 are all registered to Amazon AWB, hence the /22 range in this report. BLP disruption caught by filter log. 73.67.145.30 (talk) 16:45, 28 April 2023 (UTC)
- I've checked the three /24s separately here (165.85.64.0/24 · contribs · block · log · stalk · Robtex · whois · Google - 165.85.65.0/24 · contribs · block · log · stalk · Robtex · whois · Google - 165.85.66.0/24 · contribs · block · log · stalk · Robtex · whois · Google). While the ISP is Amazon, all three ranges are currently allocated to Palo Alto Networks. The first range, 165.85.64.0/24, appears to be used for part of their GlobalProtect VPN service per Spur's data. This seems similar to the McAfee WGCS and Zscaler ranges currently reported on this page, and any hardblock on these ranges would have some collateral on legitimate users. A softblock/{{Colocationwebhost-soft}} might be appropriate here. The other two ranges in the /22 seem to be in the same data centre, and don't seem to be part of the same service, but the filter log linked above is from an IP on the third /24 so it clearly has some use somewhere. Not sure what to recommend here, and I've not been able to easily search to see if any other IPs in the range have triggered any filters, though none have any recorded contributions. Sideswipe9th (talk) 18:17, 17 July 2023 (UTC)
209.35.227.0/24
[edit]![]() – A proxy checker has requested a second opinion on this case.
– A proxy checker has requested a second opinion on this case.
Reason: VPN. Perimeter 81. 73.67.145.30 (talk) 18:43, 15 May 2023 (UTC)
 Confirmed While the range is announced by Perimeter 81, and a large portion of it seems to be empty per Spur and Shodan, there are IP ranges within that are active on Perimeter 81's VPN product. However that product is aimed at businesses, with pricing to match. This seems similar to the Zscaler, McAfee WGCS cases that are also open at present. A softblock on the range might be appropriate however, the one contributor who was active on 15 May 2023 was using an IP that's part of their VPN range. While I've tried to pin down the exact range for just the IPs that are part of their VPN offering, it seems somewhat spread out throughout it with gaps, so it might be more expedient to just block it in its entirety. Flagging this for a 2O though, while we figure out how to handle this particular type of VPN provider. Sideswipe9th (talk) 00:22, 19 July 2023 (UTC)
Confirmed While the range is announced by Perimeter 81, and a large portion of it seems to be empty per Spur and Shodan, there are IP ranges within that are active on Perimeter 81's VPN product. However that product is aimed at businesses, with pricing to match. This seems similar to the Zscaler, McAfee WGCS cases that are also open at present. A softblock on the range might be appropriate however, the one contributor who was active on 15 May 2023 was using an IP that's part of their VPN range. While I've tried to pin down the exact range for just the IPs that are part of their VPN offering, it seems somewhat spread out throughout it with gaps, so it might be more expedient to just block it in its entirety. Flagging this for a 2O though, while we figure out how to handle this particular type of VPN provider. Sideswipe9th (talk) 00:22, 19 July 2023 (UTC)
157.167.128.0/24
[edit]![]() A user has requested a proxy check. A proxy checker will shortly look into the case.
A user has requested a proxy check. A proxy checker will shortly look into the case.
Reason: Cloud server/VPN. This is an odd one, because the IP range geolocates to Turkey, and is listed as a VPN network; but most of the edits are to Turkish-related articles. Is this some sort of corporate cloud network? 2601:1C0:4401:F60:8C11:4CC3:7E71:B4CE (talk) 20:54, 13 August 2023 (UTC)
192.189.187.125
[edit]![]() A user has requested a proxy check. A proxy checker will shortly look into the case.
A user has requested a proxy check. A proxy checker will shortly look into the case.
- 192.189.187.125 · talk · contribs · block · log · stalk · Robtex · whois · Google · ipcheck · HTTP · geo · rangeblocks · spur · shodan
Reason:Listed ISP is FedEx which is not a legitimate provider, in addition these various FedEx proxy ranges are used by a LTA and extensive sock puppeteer HaughtonBrit to block evade and push tendentious edits in various South Asian topics. Southasianhistorian8 (talk) 21:13, 3 April 2024 (UTC)
110.93.85.16 and others
[edit]![]() A user has requested a proxy check. A proxy checker will shortly look into the case.
A user has requested a proxy check. A proxy checker will shortly look into the case.
- 110.93.85.16 · talk · contribs · block · log · stalk · Robtex · whois · Google · ipcheck · HTTP · geo · rangeblocks · spur · shodan (July 2024)
- 110.93.85.239 · talk · contribs · block · log · stalk · Robtex · whois · Google · ipcheck · HTTP · geo · rangeblocks · spur · shodan (June 2024)
Reason: Questionable beauty pageant editing for some time from IPs in 110.93.85.0/24, and recent use by those noted above; spur reports both belong to a call-back proxy network. ☆ Bri (talk) 19:44, 2 July 2024 (UTC)
Automated lists and tools
[edit]- User:AntiCompositeBot/ASNBlock maintained by User:AntiCompositeBot is a list of hosting provider ranges that need assessment for blocks that is updated daily. Admins are encouraged to review the list and assess for blocks as needed. All administrators are individually responsible for any blocks they make based on that list.
- ISP Rangefinder is a tool that allows administrators to easily identify and hard block all ranges for an entire ISP. It should be used with extreme caution, but is useful for blocking known open proxy providers. All administrators are individually responsible for any blocks they make based on the results from this tool.
- IPCheck is a tool that can help provide clues about potential open proxies.
- Bullseye provides information about IPS, including clues about potential open proxies.
- whois-referral is a generic WHOIS tool.
- Range block finder finds present and past range blocks.
See also
[edit]- Subpages
- Related pages
- Policy on open proxies
- Open proxy detection
- Guide to checking open proxies
- Proxy check result templates
- Advice to users using Tor to bypass the Great Firewall
- meta:XFF project
- Sister projects (defunct)
| This is a WikiProject, an area for focused collaboration among Wikipedians. New participants are welcome; please feel free to participate!
|