Zero-day vulnerability
A zero-day (also known as a 0-day) is a vulnerability in software or hardware that is typically unknown to the vendor and for which no patch or other fix is available. The vendor thus has zero days to prepare a patch, as the vulnerability has already been described or exploited.
Despite developers' goal of delivering a product that works entirely as intended, virtually all software and hardware contains bugs. Many of these impair the security of the system and are thus vulnerabilities. Although the basis of only a minority of cyberattacks, zero-days are considered more dangerous than known vulnerabilities because there are fewer countermeasures possible.
States are the primary users of zero-day vulnerabilities, not only because of the high cost of finding or buying them, but also the significant cost of writing the attack software. Many vulnerabilities are discovered by hackers or security researchers, who may disclose them to the vendor (often in exchange for a bug bounty) or sell them to states or criminal groups. The use of zero-days increased after many popular software companies began to encrypt messages and data, meaning that the unencrypted data could only be obtained by hacking into the software before it was encrypted.
Definition
[edit]Despite developers' goal of delivering a product that works entirely as intended, virtually all software and hardware contain bugs.[1] If a bug creates a security risk, it is called a vulnerability. Vulnerabilities vary in their ability to be exploited by malicious actors. Some are not usable at all, while others can be used to disrupt the device with a denial of service attack. The most valuable allow the attacker to inject and run their own code, without the user being aware of it.[2] Although the term "zero-day" initially referred to the time since the vendor had become aware of the vulnerability, zero-day vulnerabilities can also be defined as the subset of vulnerabilities for which no patch or other fix is available.[3][4][5] A zero-day exploit is any exploit that takes advantage of such a vulnerability.[2]
Exploits
[edit]An exploit is the delivery mechanism that takes advantage of the vulnerability to penetrate the target's systems, for such purposes as disrupting operations, installing malware, or exfiltrating data.[6] Researchers Lillian Ablon and Andy Bogart write that "little is known about the true extent, use, benefit, and harm of zero-day exploits".[7] Exploits based on zero-day vulnerabilities are considered more dangerous than those that take advantage of a known vulnerability.[8][9] However, it is likely that most cyberattacks use known vulnerabilities, not zero-days.[7]
States are the primary users of zero-day exploits, not only because of the high cost of finding or buying vulnerabilities, but also the significant cost of writing the attack software. Nevertheless, anyone can use a vulnerability,[4] and according to research by the RAND Corporation, "any serious attacker can always get an affordable zero-day for almost any target".[10] Many targeted attacks[11] and most advanced persistent threats rely on zero-day vulnerabilities.[12]
The average time to develop an exploit from a zero-day vulnerability was estimated at 22 days.[13] The difficulty of developing exploits has been increasing over time due to increased anti-exploitation features in popular software.[14]
Window of vulnerability
[edit]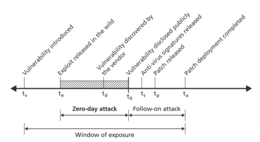
Zero-day vulnerabilities are often classified as alive—meaning that there is no public knowledge of the vulnerability—and dead—the vulnerability has been disclosed, but not patched. If the software's maintainers are actively searching for vulnerabilities, it is a living vulnerability; such vulnerabilities in unmaintained software are called immortal. Zombie vulnerabilities can be exploited in older versions of the software but have been patched in newer versions.[15]
Even publicly known and zombie vulnerabilities are often exploitable for an extended period.[16][17] Security patches can take months to develop,[18] or may never be developed.[17] A patch can have negative effects on the functionality of software[17] and users may need to test the patch to confirm functionality and compatibility.[19] Larger organizations may fail to identify and patch all dependencies, while smaller enterprises and personal users may not install patches.[17]
Research suggests that risk of cyberattack increases if the vulnerability is made publicly known or a patch is released.[20] Cybercriminals can reverse engineer the patch to find the underlying vulnerability and develop exploits,[21] often faster than users install the patch.[20]
According to research by RAND Corporation published in 2017, zero-day exploits remain usable for 6.9 years on average,[22] although those purchased from a third party only remain usable for 1.4 years on average.[13] The researchers were unable to determine if any particular platform or software (such as open-source software) had any relationship to the life expectancy of a zero-day vulnerability.[23] Although the RAND researchers found that 5.7 percent of a stockpile of secret zero-day vulnerabilities will have been discovered by someone else within a year,[24] another study found a higher overlap rate, as high as 10.8 percent to 21.9 percent per year.[25]
Countermeasures
[edit]Because, by definition, there is no patch that can block a zero-day exploit, all systems employing the software or hardware with the vulnerability are at risk. This includes secure systems such as banks and governments that have all patches up to date.[26] Security systems are designed around known vulnerabilities, and repeated exploitations of a zero-day exploit could continue undetected for an extended period of time.[17] Although there have been many proposals for a system that is effective at detecting zero-day exploits, this remains an active area of research in 2023.[27]
Many organizations have adopted defense-in-depth tactics so that attacks are likely to require breaching multiple levels of security, which makes it more difficult to achieve.[28] Conventional cybersecurity measures such as training and access control such as multifactor authentication, least-privilege access, and air-gapping makes it harder to compromise systems with a zero-day exploit.[29] Since writing perfectly secure software is impossible, some researchers argue that driving up the cost of exploits is a good strategy to reduce the burden of cyberattacks.[30]
Market
[edit]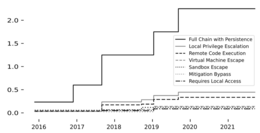
Zero-day exploits can fetch millions of dollars.[4] There are three main types of buyers:[31]
- White: the vendor, or to third parties such as the Zero Day Initiative that disclose to the vendor. Often such disclosure is in exchange for a bug bounty.[32][33][34] Not all companies respond positively to disclosures, as they can cause legal liability and operational overhead. It is not uncommon to receive cease-and-desist letters from software vendors after disclosing a vulnerability for free.[35]
- Gray: the largest[4] and most lucrative. Government or intelligence agencies buy zero-days and may use it in an attack, stockpile the vulnerability, or notify the vendor.[31] The United States federal government is one of the largest buyers.[4] As of 2013, the Five Eyes (United States, United Kingdom, Canada, Australia, and New Zealand) captured the plurality of the market and other significant purchasers included Russia, India, Brazil, Malaysia, Singapore, North Korea, and Iran. Middle Eastern countries were poised to become the biggest spenders.[36]
- Black: organized crime, which typically prefers exploit software rather than just knowledge of a vulnerability.[37] These users are more likely to employ "half-days" where a patch is already available.[38]
In 2015, the markets for government and crime were estimated at at least ten times larger than the white market.[31] Sellers are often hacker groups that seek out vulnerabilities in widely used software for financial reward.[39] Some will only sell to certain buyers, while others will sell to anyone.[38] White market sellers are more likely to be motivated by non pecuniary rewards such as recognition and intellectual challenge.[40] Selling zero day exploits is legal.[34][41] Despite calls for more regulation, law professor Mailyn Fidler says there is little chance of an international agreement because key players such as Russia and Israel are not interested.[41]
The sellers and buyers that trade in zero-days tend to be secretive, relying on non-disclosure agreements and classified information laws to keep the exploits secret. If the vulnerability becomes known, it can be patched and its value consequently crashes.[42] Because the market lacks transparency, it can be hard for parties to find a fair price. Sellers might not be paid if the vulnerability was disclosed before it was verified, or if the buyer declined to purchase it but used it anyway. With the proliferation of middlemen, sellers could never know to what use the exploits could be put.[43] Buyers could not guarantee that the exploit was not sold to another party.[44] Both buyers and sellers advertise on the dark web.[45]
Research published in 2022 based on maximum prices paid as quoted by a single exploit broker found a 44 percent annualized inflation rate in exploit pricing. Remote zero-click exploits could fetch the highest price, while those that require local access to the device are much cheaper.[46] Vulnerabilities in widely used software are also more expensive.[47] They estimated that around 400 to 1,500 people sold exploits to that broker and they made around $5,500 to $20,800 annually.[48]
Disclosure and stockpiling
[edit]As of 2017[update], there is an ongoing debate as to whether the United States should disclose the vulnerabilities it is aware of, so that they can be patched, or keep them secret for its own use.[49] Reasons that states keep an vulnerability secret include wanting to use it offensively, or defensively in penetration testing.[10] Disclosing the vulnerability reduces the risk that consumers and all users of the software will be victimized by malware or data breaches.[1]
The phases of zero-day vulnerability disclosure, along with a typical timeline, are as follows:
- Discovery: A researcher identifies the vulnerability, marking "Day 0."
- Reporting: The researcher notifies the vendor or a third party, starting remediation efforts.
- Patch Development: The vendor develops a fix, which can take weeks to months depending on the complexity.
- Public Disclosure: Once a patch is released, details are shared publicly. If no patch is issued within an agreed period (commonly 90 days), some researchers disclose it to push for action.
History
[edit]Zero-day exploits increased in significance after services such as Apple, Google, Facebook, and Microsoft encrypted servers and messages, meaning that the most feasible way to access a user's data was to intercept it at the source before it was encrypted.[26] One of the best-known use of zero-day exploits was the Stuxnet worm, which used four zero-day vulnerabilities to damage Iran's nuclear program in 2010.[7] The worm showed what could be achieved by zero-day exploits, unleashing an expansion in the market.[36]
The United States National Security Agency (NSA) increased its search for zero-day vulnerabilities after large tech companies refused to install backdoors into the software, tasking the Tailored Access Operations (TAO) with discovering and purchasing zero-day exploits.[50] In 2007, former NSA employee Charlie Miller publicly revealed for the first time that the United States government was buying zero-day exploits.[51] Some information about the NSA involvement with zero-days was revealed in the documents leaked by NSA contractor Edward Snowden in 2013, but details were lacking.[50] Reporter Nicole Perlroth concluded that "either Snowden’s access as a contractor didn’t take him far enough into the government’s systems for the intel required, or some of the government’s sources and methods for acquiring zero-days were so confidential, or controversial, that the agency never dared put them in writing".[52]
One of the most infamous vulnerabilities discovered after 2013, Heartbleed (CVE-2014-0160), was not a zero-day when publicly disclosed but underscored the critical impact that software bugs can have on global cybersecurity. This flaw in the OpenSSL cryptographic library could have been exploited as a zero-day prior to its discovery, allowing attackers to steal sensitive information such as private keys and passwords.[53]
In 2016 the hacking group known as Shadow Brokers released a trove of sophisticated zero-day exploits reportedly stolen from the United States National Security Agency (NSA). These included tools such as EternalBlue, which leveraged a vulnerability in Microsoft Windows' Server Message Block (SMB) protocol. EternalBlue was later weaponized in high-profile attacks like WannaCry and NotPetya, causing widespread global damage and highlighting the risks of stockpiling vulnerabilities.[54]
The year 2020 saw one of the most sophisticated cyber espionage campaigns to date, in which attackers exploited multiple vulnerabilities, including zero-day vulnerabilities, to compromise SolarWinds' Orion software. This allowed access to numerous government and corporate networks.[55]
In 2021 Chinese state-sponsored group, Hafnium, exploited zero-day vulnerabilities in Microsoft Exchange Server to conduct cyber espionage. Known as ProxyLogon, these flaws allowed attackers to bypass authentication and execute arbitrary code, compromising thousands of systems globally.[56]
In 2022 the spyware Pegasus, developed by Israel's NSO Group, was found to exploit zero-click vulnerabilities in messaging apps like iMessage and WhatsApp. These exploits allowed attackers to access targets' devices without requiring user interaction, heightening concerns over surveillance and privacy.[57]
References
[edit]- ^ a b Ablon & Bogart 2017, p. 1.
- ^ a b Ablon & Bogart 2017, p. 2.
- ^ Ablon & Bogart 2017, pp. iii, 2.
- ^ a b c d e Sood & Enbody 2014, p. 1.
- ^ Perlroth 2021, p. 7.
- ^ Strout 2023, p. 23.
- ^ a b c Ablon & Bogart 2017, p. 3.
- ^ Sood & Enbody 2014, p. 24.
- ^ Bravo & Kitchen 2022, p. 11.
- ^ a b Ablon & Bogart 2017, p. xiv.
- ^ Sood & Enbody 2014, pp. 2–3, 24.
- ^ Sood & Enbody 2014, p. 4.
- ^ a b Ablon & Bogart 2017, p. xiii.
- ^ Perlroth 2021, p. 142.
- ^ Ablon & Bogart 2017, p. xi.
- ^ Ablon & Bogart 2017, p. 8.
- ^ a b c d e Sood & Enbody 2014, p. 42.
- ^ Strout 2023, p. 26.
- ^ Libicki, Ablon & Webb 2015, p. 50.
- ^ a b Libicki, Ablon & Webb 2015, pp. 49–50.
- ^ Strout 2023, p. 28.
- ^ Ablon & Bogart 2017, p. x.
- ^ Ablon & Bogart 2017, pp. xi–xii.
- ^ Ablon & Bogart 2017, p. x: "For a given stockpile of zero-day vulnerabilities, after a year, approximately 5.7 percent have been discovered by an outside entity."
- ^ Leal, Marcelo M.; Musgrave, Paul (2023). "Backwards from zero: How the U.S. public evaluates the use of zero-day vulnerabilities in cybersecurity". Contemporary Security Policy. 44 (3): 437–461. doi:10.1080/13523260.2023.2216112. ISSN 1352-3260.
- ^ a b Perlroth 2021, p. 8.
- ^ Ahmad et al. 2023, p. 10733.
- ^ Strout 2023, p. 24.
- ^ Libicki, Ablon & Webb 2015, p. 104.
- ^ Dellago, Simpson & Woods 2022, p. 41.
- ^ a b c Libicki, Ablon & Webb 2015, p. 44.
- ^ Dellago, Simpson & Woods 2022, p. 33.
- ^ O'Harrow 2013, p. 18.
- ^ a b Libicki, Ablon & Webb 2015, p. 45.
- ^ Strout 2023, p. 36.
- ^ a b Perlroth 2021, p. 145.
- ^ Libicki, Ablon & Webb 2015, pp. 44, 46.
- ^ a b Libicki, Ablon & Webb 2015, p. 46.
- ^ Sood & Enbody 2014, p. 116.
- ^ Libicki, Ablon & Webb 2015, pp. 46–47.
- ^ a b Gooding, Matthew (19 July 2022). "Zero day vulnerability trade is lucrative but risky". Tech Monitor. Retrieved 4 April 2024.
- ^ Perlroth 2021, p. 42.
- ^ Perlroth 2021, p. 57.
- ^ Perlroth 2021, p. 58.
- ^ Sood & Enbody 2014, p. 117.
- ^ Dellago, Simpson & Woods 2022, pp. 31, 41.
- ^ Libicki, Ablon & Webb 2015, p. 48.
- ^ Dellago, Simpson & Woods 2022, p. 42: "The number of independent active sellers (between 400[31] and 1500[35] individuals) ... 2015,[35] suggests an annual pay of $5.5k - 20.8k per researcher."
- ^ Ablon & Bogart 2017, p. iii.
- ^ a b Perlroth 2021, p. 9.
- ^ Perlroth 2021, pp. 60, 62.
- ^ Perlroth 2021, p. 10.
- ^ "Heartbleed: Serious OpenSSL zero day vulnerability revealed". ZDNet. Archived from the original on 2024-10-04. Retrieved 2024-11-29.
- ^ "The Shadow Brokers publishing the NSA vulnerabilities". Cyberlaw. Archived from the original on 2024-02-27. Retrieved 2024-11-29.
- ^ "SolarWinds hack explained: Everything you need to know". TechTarget. Archived from the original on 2024-10-05. Retrieved 2024-11-29.
- ^ "Businesses urged to act fast against ProxyLogon attack on Microsoft Exchange Server". S-RM. Archived from the original on 2024-11-29. Retrieved 2024-11-29.
- ^ "NSO Group's Pegasus Spyware Returns in 2022 with a Trio of iOS 15 and iOS 16 Zero-Click Exploit Chains". Citizenlab. Archived from the original on 2024-09-27. Retrieved 2024-11-29.
Sources
[edit]- Ablon, Lillian; Bogart, Andy (2017). Zero Days, Thousands of Nights: The Life and Times of Zero-Day Vulnerabilities and Their Exploits (PDF). Rand Corporation. ISBN 978-0-8330-9761-3.
- Ahmad, Rasheed; Alsmadi, Izzat; Alhamdani, Wasim; Tawalbeh, Lo’ai (2023). "Zero-day attack detection: a systematic literature review". Artificial Intelligence Review. 56 (10): 10733–10811. doi:10.1007/s10462-023-10437-z. ISSN 1573-7462.
- Bravo, Cesar; Kitchen, Darren (2022). Mastering Defensive Security: Effective techniques to secure your Windows, Linux, IoT, and cloud infrastructure. Packt Publishing. ISBN 978-1-80020-609-0.
- Dellago, Matthias; Simpson, Andrew C.; Woods, Daniel W. (2022). "Exploit Brokers and Offensive Cyber Operations". The Cyber Defense Review. 7 (3): 31–48. ISSN 2474-2120. JSTOR 48682321.
- Libicki, Martin C.; Ablon, Lillian; Webb, Tim (2015). The Defender’s Dilemma: Charting a Course Toward Cybersecurity (PDF). Rand Corporation. ISBN 978-0-8330-8911-3.
- O'Harrow, Robert (2013). Zero Day: The Threat In Cyberspace. Diversion Books. ISBN 978-1-938120-76-3.
- Perlroth, Nicole (2021). This Is How They Tell Me the World Ends: The Cyberweapons Arms Race. Bloomsbury Publishing. ISBN 978-1-5266-2983-8.
- Sood, Aditya; Enbody, Richard (2014). Targeted Cyber Attacks: Multi-staged Attacks Driven by Exploits and Malware. Syngress. ISBN 978-0-12-800619-1.
- Strout, Benjamin (2023). The Vulnerability Researcher's Handbook: A comprehensive guide to discovering, reporting, and publishing security vulnerabilities. Packt Publishing. ISBN 978-1-80324-356-6.
